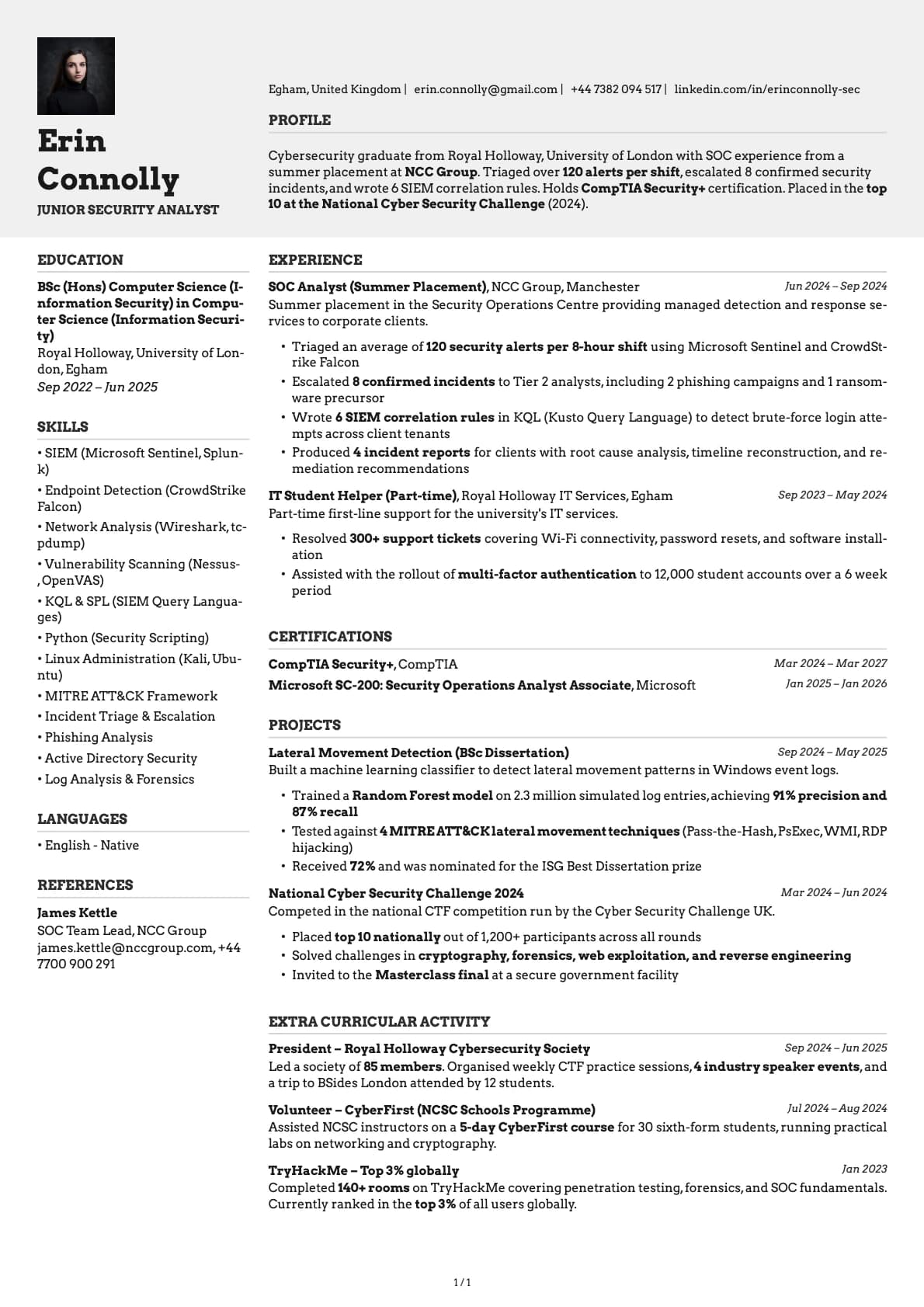
Junior Security Analyst Resume Example
A junior security analyst resume example with SOC experience, CompTIA Security+ certification, and incident triage from a Cybersecurity BSc graduate.
Laddro Team
Overview
Cybersecurity hiring is growing faster than almost any other technology discipline, and SOC analyst roles are the most common entry point. Employers want candidates who understand threat detection, can triage alerts efficiently, and hold at least one recognised certification. Hands-on lab experience and CTF (Capture the Flag) competition results help bridge the gap between academic knowledge and operational readiness.
This resume belongs to Erin Connolly, a Cybersecurity graduate from Royal Holloway, University of London. She completed a summer placement in the SOC at NCC Group, holds CompTIA Security+, and placed in the top 10 at the National Cyber Security Challenge. Her resume works because it translates academic security knowledge into operational, measurable experience.
What Makes This Resume Work
The SOC placement at NCC Group is a powerful credential. NCC Group is one of the UK's most recognised cybersecurity consultancies. Erin describes her role in operational terms: alerts triaged, incidents escalated, and SIEM queries written. This is the language SOC managers use.
CompTIA Security+ is featured prominently. This certification is widely requested in junior security analyst job descriptions. Having it before graduating signals that Erin has validated her knowledge against an industry-recognised standard.
CTF competition results demonstrate practical skill. Placing in the top 10 at a national competition shows that Erin can apply security knowledge under pressure, solving real challenges rather than just answering exam questions.
Incident triage numbers are quantified. Reviewing 120+ alerts per shift, escalating 8 confirmed incidents, and writing 6 SIEM correlation rules are the kind of operational metrics that prove hands-on capability.
Key Takeaways
Junior security analyst resumes should lead with certifications (CompTIA Security+, or equivalent), SOC experience (even a short placement), and any CTF results. Describe your alert triage volume, escalation decisions, and SIEM tool experience. Mention specific tools (Splunk, Sentinel, CrowdStrike) by name. Practical, operational language matters more than theoretical security knowledge at this level.
Was this resume example helpful?
Rate this example to help us create better content for you.
4.8 average from 131 ratingsRelated resume examples

Architectural Assistant
An architectural assistant resume example with RIBA Part 1 qualification, AutoCAD drawings, and residential project experience from a Part 1 graduate.

Assistant Psychologist
An assistant psychologist resume example for psychology graduates showing how to present research experience, clinical exposure, and therapy skills for NHS Band 4 roles.

Café Supervisor
A café supervisor resume example for someone who worked up from barista without a degree. See how to present your customer service, team management, and food hygiene credentials.

Court Usher
A court usher resume example for candidates entering the court service. See how to present your customer service skills, security awareness, and knowledge of court procedures.

Cruise Ship Crew Member
A cruise ship crew resume example for hospitality graduates entering the cruise industry. See how to present your STCW certification, onboard experience, and customer service skills.

Customer Service Team Leader
A customer service team leader resume example with management degree, contact centre experience, and team performance metrics.

Dental Nurse
A dental nurse resume example for newly qualified candidates showing how to present GDC registration, clinical experience, and chairside skills for your first dental nursing role.

Electrician's Mate
An electrician's mate resume example for apprentice electricians entering the trade. See how to present your City & Guilds, ECS card, and practical wiring experience.

ESOL Tutor
A graduate ESOL tutor resume example with EFL teaching practice, CELTA, and multilingual classroom experience. See how to present your qualifications for ESOL teaching roles.

Gallery Assistant
A gallery assistant resume example with exhibition installation experience, visitor engagement numbers, and Fine Art credentials from a recent BA graduate.

Graduate Accountant
A graduate accountant resume example for recent graduates. See how to present your accounting degree, Excel skills, and placement experience to secure your first role.

Graduate Actuary Trainee
A graduate actuary trainee resume example with Hymans Robertson internship and IFoA exam passes.

Graduate Aerospace Engineer
A graduate aerospace engineer resume example with CFD analysis skills, Airbus placement experience, and RAeS membership.

Graduate Archaeologist
A graduate archaeologist resume example with commercial excavation experience, single-context recording, and CIfA membership.

Graduate Banking Analyst
A graduate banking analyst resume example with Barclays ECM internship and financial modelling skills.

Graduate Biomedical Scientist
A graduate biomedical scientist resume example with NHS lab placement experience, HCPC registration, and sample processing numbers.

Graduate Building Services Engineer
A graduate building services engineer resume example with MEP consultancy experience, energy modelling skills, and CIBSE membership.

Graduate Building Surveyor
A graduate building surveyor resume example with chartered practice placement and building inspection experience.

Graduate Civil Engineer
A graduate civil engineer resume example for recent graduates. See how to present your engineering degree, placement experience, and technical skills to land your first role.

Graduate Civil Servant
A graduate civil servant resume example with Department for Education placement and policy support experience.

Graduate Customs Officer
A graduate customs officer resume example with HMRC placement and customs compliance experience.

Graduate Dental Hygienist
A graduate dental hygienist resume example with GDC registration, clinical patient numbers, and periodontal treatment experience for new graduates.

Graduate Electrical Engineer
A graduate electrical engineer resume example with power systems placement experience, IET membership, and MATLAB proficiency.

Graduate Film Production Assistant
A graduate film production assistant resume example. See how to present runner experience, production coordination, and on-set skills to break into the film industry.

Graduate Financial Analyst
A graduate financial analyst resume example for recent graduates. See how to present your financial modelling skills, Excel expertise, and internship experience to land an analyst role.

Graduate Firefighter
A graduate firefighter resume example showing how to combine a Fire and Rescue Science degree with lifeguarding and community safety volunteering.

Graduate Food Scientist
A graduate food scientist resume example with NPD placement experience, HACCP knowledge, and quality control test numbers for food science graduates.

Graduate Forensic Scientist
A graduate forensic scientist resume example with police lab placement experience, DNA profiling skills, and chain of custody knowledge.

Graduate Geologist
A graduate geologist resume example with geotechnical placement experience, borehole logging, and Geological Society membership.

Graduate Hotel Manager Trainee
A graduate hotel manager trainee resume example with InterContinental placement and multi-department experience.

Graduate HR Assistant
A graduate HR assistant resume example for recent graduates. See how to present your people skills, admin experience, and HR knowledge to land your first human resources role.

Graduate Insurance Underwriter
A graduate insurance underwriter resume example with Zurich internship experience and commercial insurance knowledge.

Graduate Investment Analyst
A graduate investment analyst resume example with Schroders internship experience and equity research skills.

Graduate IT Consultant
A graduate IT consultant resume example. See how to present consulting experience, stakeholder management, and business analysis skills to land your first IT consulting role.

Graduate IT Support Analyst
A graduate IT support analyst resume example. See how to present helpdesk experience, ITIL certification, and service desk metrics to land your first IT support role.

Graduate Journalist
A graduate journalist resume example showing how to present published work, newsroom experience, and multimedia skills to land your first reporting role.

Graduate Land Surveyor
A graduate land surveyor resume example. See how to present site survey experience, GPS/GNSS skills, and CAD output to land your first surveying role.

Graduate Legal Secretary
A graduate legal secretary resume example. See how to present typing speed, legal document preparation, and solicitor support experience to land your first legal secretary role.

Graduate Library Assistant
A graduate library assistant resume example. See how to present library experience, cataloguing skills, and event programming to land your first library role.

Graduate Management Trainee
A graduate management trainee resume example with retail placement experience and team leadership skills.

Graduate Marine Biologist
A graduate marine biologist resume example with research placement experience, dive survey qualifications, and intertidal survey numbers.

Graduate Mechanical Engineer
A graduate mechanical engineer resume example with Year in Industry placement, SolidWorks proficiency, and IMechE membership on the IEng pathway.

Graduate Midwife
A graduate midwife resume example with birth attendance numbers, NMBI registration, and clinical placement hours for newly qualified midwives.

Graduate Museum Assistant
A graduate museum assistant resume example. See how to present collections experience, gallery tours, and museum studies qualifications to land your first museum role.

Graduate Nurse
A graduate nurse resume example for recently qualified nurses. See how to present your clinical placements, patient care experience, and NMC registration to land your first nursing role.

Graduate Nursery Practitioner
A graduate nursery practitioner resume example with EYFS experience, key person responsibilities, and Level 3 Early Years Educator qualification.

Graduate Operations Analyst
A graduate operations analyst resume example with Jaguar Land Rover placement and data analysis skills.

Graduate Optometrist
A graduate optometrist resume example with pre-registration experience, GOC registration, and eye examination numbers for newly qualifying optometrists.

Graduate Paramedic
A graduate paramedic resume example with frontline placement hours, HCPC registration, and emergency call numbers for newly qualified paramedics.

Graduate Pension Administrator
A graduate pension administrator resume example with Mercer internship and benefit calculation experience.

Graduate Planner
A graduate planner resume example for town planning MA graduates. See how to present your RTPI accredited degree, planning applications experience, and policy knowledge.

Graduate Police Officer
A graduate police officer resume example showing how to turn retail security, victim support volunteering, and a criminology degree into a strong PSNI application.

Graduate Policy Analyst
A graduate policy analyst resume example with Northern Ireland Assembly internship and public policy research experience.

Graduate Probation Officer
A graduate probation officer resume example with prison placement experience and risk assessment skills.

Graduate Process Engineer
A graduate process engineer resume example with chemical plant placement experience, HAZOP participation, and IChemE membership.

Graduate Production Planner
A graduate production planner resume example with Rolls-Royce placement and SAP scheduling experience.

Graduate Property Manager
A graduate property manager resume example with Savills placement and residential lettings experience.

Graduate Quantity Surveyor
A graduate quantity surveyor resume example with a construction placement year. See how to present valuations, measurement skills, and NEC contract experience.

Graduate Recruitment Consultant
A graduate recruitment consultant resume example for recent graduates. Learn how to present your communication skills, sales experience, and people skills for recruitment roles.

Graduate Restaurant Manager Trainee
A graduate restaurant manager trainee resume example. See how to present shift leadership, customer satisfaction, and hospitality qualifications to land your first management trainee role.

Graduate Social Worker
A graduate social worker resume example with statutory placement experience, caseload numbers, and Social Work England registration for NQSWs.

Graduate Speech and Language Therapist
A graduate speech and language therapist resume example with clinical placement hours, HCPC registration, and paediatric caseload numbers.

Graduate Structural Engineer
A graduate structural engineer resume example with consultancy placement experience, Eurocode design skills, and IStructE membership.

Graduate Town Planner
A graduate town planner resume example with local authority placement experience and RTPI accredited degree.

Graduate Transport Planner
A graduate transport planner resume example. See how to present transport assessment experience, traffic survey data, and TPS membership to land your first transport planning role.

Graduate Veterinary Nurse
A graduate veterinary nurse resume example with RCVS registration, surgical assist numbers, and clinical placement hours for newly qualified RVNs.

Groundskeeper
A groundskeeper resume example showing how to combine a horticulture degree with council grounds work and a historic garden placement.

Gym Instructor
A gym instructor resume example showing how to combine a Level 2 fitness qualification with competitive swimming and strong member satisfaction scores.

Healthcare Assistant
A healthcare assistant resume example for candidates with NVQ Level 3 in Health and Social Care, showing how to present ward experience and patient care skills for NHS Band 3/4 roles.

Immigration Caseworker
An immigration caseworker resume example for immigration law graduates. See how to present your OISC registration, casework experience, and visa application knowledge.

IT Support Technician
An IT support technician resume example with ticket resolution stats, CompTIA certification, and helpdesk experience from an IT graduate starting their career.

Junior Accounts Assistant
A junior accounts assistant resume example with accountancy firm placement and AAT Level 3 qualification.

Junior Animator
A junior animator resume example for recent graduates. See how to present showreels, studio experience, and festival selections to land your first animation role.

Junior A&R Assistant
A junior A&R assistant resume example with music business degree, label internship, and artist scouting experience for 2026.

Junior Architectural Technologist
A junior architectural technologist resume example for graduates. See how to present Revit skills, BIM experience, and technical drawing output to land your first architectural technology role.

Junior Auditor
A junior auditor resume example with Mazars internship experience and accounts administration background.

Junior Automation Tester
A junior automation tester resume example for graduates. See how to present test automation scripts, CI/CD integration, and ISTQB certification to land your first automation testing role.

Junior Automotive Engineer
A junior automotive engineer resume example with OEM placement experience, vehicle testing data, and Formula Student achievements.

Junior Backend Developer
A junior backend developer resume example with REST API projects, PostgreSQL experience, and deployed services from a Computer Science BSc graduate entering development.

Junior Bank Associate
A junior bank associate resume example for banking graduates. See how to present your compliance knowledge, customer service skills, and internship experience.

Junior Biomedical Engineer
A junior biomedical engineer resume example with medical device R&D experience, ISO standards knowledge, and research publications.

Junior Bricklayer
A junior bricklayer resume example for NVQ qualified bricklayers entering the trade. See how to present your bricklaying skills, CSCS card, and site experience.

Junior Business Analyst
A junior business analyst resume example for career changers. See how to use retail management and a business degree to break into business analysis.

Junior Business Development Associate
A junior business development associate resume example for entrepreneurship graduates. See how cold outreach metrics and startup experience win interviews.

Junior CAD Technician
A junior CAD technician resume example with HND qualification, AutoCAD and Revit proficiency, and architectural practice experience.

Junior Care Coordinator
A junior care coordinator resume example with domiciliary care experience, rota management numbers, and CQC compliance for new coordinators.

Junior Carpenter
A junior carpenter resume example for carpentry apprenticeship graduates. See how to present your City & Guilds, site joinery experience, and CSCS card details.

Junior Charity Fundraiser
A junior charity fundraiser resume example with Irish Cancer Society internship and event coordination experience.

Junior Chemical Engineer
A junior chemical engineer resume example with industrial placement experience, process improvement savings, and IChemE membership for graduates.

Junior Cloud Engineer
A junior cloud engineer resume example for graduates. Learn how to present AWS experience, Terraform skills, and cloud certifications to land your first cloud engineering role.

Junior Communications Officer
A junior communications officer resume example for graduates. See how to present internal comms, content writing, and stakeholder engagement experience to land your first comms role.

Junior Compliance Officer
A junior compliance officer resume example with insurance compliance internship experience and AML knowledge.

Junior Conservation Officer
A junior conservation officer resume example with wildlife trust placement experience, volunteer coordination, and habitat management skills.

Junior Consultant
A junior consultant resume example with management degree, Big Four internship, and client facing project delivery experience.

Junior Content Writer
A junior content writer resume example for recent graduates. See how to showcase your writing portfolio, SEO knowledge, and published work to land your first content role.

Junior Copywriter
A junior copywriter resume example for English graduates. See how to present freelance writing, student newspaper experience, and a portfolio to land your first agency or in-house role.

Junior Council Officer
A junior council officer resume example showing how to turn a council placement, student politics, and a public policy degree into a local government career.

Junior Court Clerk
A junior court clerk resume example for law graduates. See how to present court administration experience, case file management, and HMCTS placement work to land your first court clerk role.

Junior Credit Analyst
A junior credit analyst resume example with Bank of Ireland internship experience and financial analysis skills.

Junior Criminology Caseworker
A junior criminology caseworker resume example for graduates. See how to present probation experience, risk assessment skills, and mentoring work to land your first caseworker role.

Junior Cybersecurity Analyst
A junior cybersecurity analyst resume example for graduates. See how to present SOC experience, CTF competitions, and Security+ certification to land your first cyber role.

Junior Data Analyst
A junior data analyst resume example for recent graduates. See how to showcase your SQL skills, Python projects, and analytical experience to land your first analyst role.

Junior Data Scientist
A junior data scientist resume example with Python projects, model accuracy metrics, and published research from a Data Science MSc graduate entering the field.

Junior Database Administrator
A junior database administrator resume example for graduates. See how to present SQL skills, performance tuning, and database management experience to land your first DBA role.

Junior DevOps Engineer
A junior DevOps engineer resume example for graduates. See how to present CI/CD experience, cloud certifications, and infrastructure projects to land your first DevOps role.

Junior Dietitian
A junior dietitian resume example with NHS clinical placement experience, HCPC registration, and patient caseload numbers for new graduates.

Junior Digital Commerce Executive
A junior digital commerce executive resume example showing how an e-commerce graduate used Shopify internships and campaign metrics to land a first role.

Junior Diplomat
A junior diplomat resume example showing how to combine an FCDO internship, a year at Sciences Po, and Model UN leadership into a Fast Stream application.

Junior Economic Analyst
A junior economic analyst resume example with government internship experience and strong quantitative skills.

Junior Electrical Engineer
A junior electrical engineer resume example with power systems placement experience, AutoCAD skills, and Engineers Ireland membership.

Junior Energy Engineer
A junior energy engineer resume example with renewable energy placement experience, solar PV design skills, and Energy Institute membership.

Junior Environmental Consultant
A junior environmental consultant resume example with ecological survey experience, PEA report writing, and GIS mapping skills for graduates.

Junior Environmental Engineer
A junior environmental engineer resume example with EIA experience, SuDS design, and contaminated land site investigation numbers.

Junior Estate Agent
A junior estate agent resume example with sales negotiator experience and ARLA Propertymark qualification.

Junior Events Coordinator
A junior events coordinator resume example with hotel placement experience and corporate event management skills.

Junior Events Planner
A junior events planner resume example for events management graduates. See how to present your event coordination experience, guest counts, budgets, and vendor management skills.

Junior Executive PA
A junior executive PA resume example with business administration degree, C-suite support experience, and diary management skills.

Junior Export Coordinator
A junior export coordinator resume example with placement experience in automotive exports and bilingual skills.

Junior Facilities Coordinator
A junior facilities coordinator resume example with facilities management degree, building services experience, and IWFM qualification.

Junior Fashion Buyer
A junior fashion buyer resume example for fashion business graduates. See how retail experience and trend forecasting skills help you land a buying role.

Junior Fashion Designer
A junior fashion designer resume example for recent graduates. See how to present collections, internship experience, and technical skills to land your first design role.

Junior Financial Controller
A junior financial controller resume example with Carnival UK placement and management accounting experience.

Junior Fire Safety Engineer
A junior fire safety engineer resume example with fire modelling experience, BS 9999 knowledge, and IFE membership for graduates.

Junior Fleet Coordinator
A junior fleet coordinator resume example for graduates. See how to present fleet management, route planning, and vehicle compliance experience to land your first fleet coordination role.

Junior Food Inspector
A junior food inspector resume example showing how to leverage QA experience in food manufacturing, HACCP training, and a food science degree.

Junior Food Technologist
A junior food technologist resume example for graduates. See how to present product development, quality testing, and food safety experience to land your first food technology role.

Junior Freight Forwarder
A junior freight forwarder resume example for logistics graduates entering international freight. See how to present your customs documentation, Incoterms knowledge, and freight operations experience.

Junior Frontend Developer
A junior frontend developer resume example for recent graduates. Learn how to present your React projects, responsive design skills, and coding experience to get your first dev job.

Junior Game Artist
A junior game artist resume example with 3D character models, game jam entries, and portfolio highlights from a Game Art BA graduate breaking into the industry.

Junior Game Developer
A junior game developer resume example with Unity projects, published games, and game jam wins from a Game Development BSc graduate entering the games industry.

Junior GIS Analyst
A junior GIS analyst resume example with local authority placement experience, spatial analysis, and Python scripting skills for geography graduates.

Junior Graphic Designer
A junior graphic designer resume example for recent graduates. Learn how to present your portfolio, design tools, and freelance work to land your first design role.

Junior Health and Safety Officer
A junior health and safety officer resume example with Balfour Beatty placement and NEBOSH qualification.

Junior Housing Officer
A junior housing officer resume example with housing association placement and tenant management experience.

Junior Illustrator
A junior illustrator resume example for graduates. See how to present freelance commissions, agency experience, and published work to land your first illustration role.

Junior Immigration Adviser
A junior immigration adviser resume example for law graduates. See how to present asylum casework, OISC qualification, and client support experience to land your first immigration advisory role.

Junior Industrial Engineer
A junior industrial engineer resume example with lean manufacturing placement experience, time study skills, and Six Sigma Yellow Belt.

Junior Interior Designer
A junior interior designer resume example for graduates. Learn how to present studio placement experience, CAD skills, and design awards to land your first interior design role.

Junior IT Project Manager
A junior IT project manager resume example with agile delivery experience, stakeholder management, and PRINCE2 Foundation from an IT graduate entering project management.

Junior Jewellery Designer
A junior jewellery designer resume example featuring CAD renders, bench skills, and collection launches from a Jewellery Design BA graduate entering the trade.

Junior Laboratory Technician
A junior lab technician resume example with pharmaceutical lab internship experience, HPLC skills, and GMP compliance for chemistry graduates.

Junior Learning Designer
A junior learning designer resume example with e-learning module numbers, Articulate 360 skills, and corporate training experience for new graduates.

Junior Legal Researcher
A junior legal researcher resume example for human rights law LLB graduates. See how to present your legal research skills, case analysis experience, and advocacy work.

Junior Logistics Coordinator
A junior logistics coordinator resume example with brewery distribution placement and route planning experience.

Junior Manufacturing Engineer
A junior manufacturing engineer resume example with aerospace placement experience, CNC skills, and cycle time reduction achievements.

Junior Marketing Coordinator
A junior marketing coordinator resume example for graduates entering the field. See how to turn retail work, volunteering, and a marketing degree into a strong application.

Junior Marketing Executive
A junior marketing executive resume example for recent graduates. See how to showcase social media skills, campaign results, and agency experience effectively.

Junior Materials Engineer
A junior materials engineer resume example with metallurgical testing experience, SEM analysis skills, and IOM3 membership.

Junior Mechanical Engineer
A junior mechanical engineer resume example with a year in industry placement. See how to present CAD skills, FEA experience, and engineering projects on your graduate CV.

Junior Mechatronics Engineer
A junior mechatronics engineer resume example with PLC programming experience, SolidWorks proficiency, and an industrial automation placement.

Junior Mental Health Worker
A junior mental health worker resume example with voluntary placement experience, assessment tools, and youth support numbers for psychology graduates.

Junior ML Engineer
A junior ML engineer resume example with deployed models, TensorFlow projects, and AWS SageMaker experience from an AI and ML MSc graduate starting their career.

Junior Mobile Developer
A junior mobile developer resume example for graduates. See how to present published apps, App Store downloads, and mobile internship experience to land your first mobile dev role.

Junior Mortgage Adviser
A junior mortgage adviser resume example with Nationwide placement experience and CeMAP qualification in progress.

Junior Motion Designer
A junior motion designer resume example with After Effects projects, client animations, and showreel details from a Motion Graphics BA graduate entering the field.

Junior Network Engineer
A junior network engineer resume example with CCNA, an MSP apprenticeship, and a home lab. See how to present networking skills and certifications for your first engineering role.

Junior Occupational Therapist
A junior occupational therapist resume example with clinical placement experience, HCPC registration, and real patient outcome numbers for new graduates.

Junior Office Manager
A junior office manager resume example with professional services placement and facilities management experience.

Junior Officer (Armed Forces)
A junior officer resume example for armed forces graduates transitioning from Sandhurst or the commissioning course. See how to present your military leadership, operational deployments, and command experience.

Junior Operations Coordinator
A junior operations coordinator resume example for operations management graduates. See how logistics experience and process improvements impress employers.

Junior Painter & Decorator
A junior painter and decorator resume example for NVQ qualified painters. See how to present your decorating skills, site experience, and CSCS card details.

Junior Paralegal
A junior paralegal resume example with litigation internship experience and legal research skills.

Junior Payroll Administrator
A junior payroll administrator resume example with Morrisons placement experience and Sage Payroll skills.

Junior Personal Trainer
A junior personal trainer resume example showing how to combine a sport science degree, Level 3 PT qualification, and gym floor experience at PureGym.

Junior Photographer
A junior photographer resume example for graduates. See how to present freelance work, studio experience, and published images to land your first photography role.

Junior Planning Consultant
A junior planning consultant resume example for graduates. See how to present planning application experience, policy analysis, and RTPI membership to land your first planning role.

Junior Podcast Producer
A junior podcast producer resume example for graduates. See how to present audio production skills, download numbers, and broadcasting experience to land your first podcast role.

Junior Policy Officer
A junior policy officer resume example for public administration graduates. See how to present research skills, briefing writing, and council placement experience.

Junior PR Executive
A junior PR executive resume example for recent graduates. See how to showcase media placements, event coordination, and communication skills to land your first PR role.

Junior Process Engineer
A junior process engineer resume example with oil and gas internship experience, HYSYS modelling, and HAZOP participation for graduates.

Junior Procurement Officer
A junior procurement officer resume example with Tata Steel placement experience and CIPS qualification.

Junior Product Designer
A junior product designer resume example with UX research projects, Figma prototypes, and usability test results from a Product Design BSc at Loughborough.

Junior Product Support Engineer
A junior product support engineer resume example for graduates. See how to present ticket resolution metrics, knowledge base work, and technical troubleshooting to land your first support engineering role.

Junior Project Coordinator
A junior project coordinator resume example for recent graduates. Learn how to present your organisational skills, team projects, and coordination experience to get hired.

Junior Public Health Officer
A junior public health officer resume example for public health graduates showing how to present epidemiology skills, data analysis experience, and health promotion projects for local authority and NHS roles.

Junior QA Tester
A junior QA tester resume example for graduates. Learn how to present testing experience, bug tracking skills, and ISTQB certification to land your first QA role.

Junior Quality Assurance Analyst
A junior QA analyst resume example with test automation experience, bug counts, and Selenium skills for computing graduates.

Junior Diagnostic Radiographer
A junior radiographer resume example with HCPC registration, examination numbers, and CT experience for newly qualified diagnostic radiographers.

Junior Retail Buyer
A junior retail buyer resume example with John Lewis placement experience and womenswear buying skills.

Junior Risk Analyst
A junior risk analyst resume example with banking internship experience and strong quantitative skills.

Junior Robotics Engineer
A junior robotics engineer resume example with ROS programming experience, computer vision skills, and a university robotics competition win.

Junior Sales Representative
A junior sales representative resume example for recent graduates. Learn how to present your target achievements, customer experience, and persuasion skills to land your first sales role.

Junior School Counsellor
A graduate school counsellor resume example with therapeutic placement hours, safeguarding, and pupil wellbeing experience. See how to present your training for school counselling roles.

Junior Shipping Agent
A junior shipping agent resume example for maritime studies graduates. See how to present your port operations knowledge, vessel documentation, and shipping line experience.

Junior Social Media Manager
A junior social media manager resume example for recent graduates. Learn how to present your content creation skills, analytics knowledge, and platform growth to get hired.

Junior Software Developer
A junior software developer resume example for recent graduates. See how to present personal projects, technical skills, and internship experience to land your first dev role.

Junior Software Engineer
A junior software engineer resume example with deployed projects, GitHub contributions, and agile sprint experience from a Software Engineering BEng graduate.

Junior Sound Engineer
A junior sound engineer resume example for graduates. Learn how to present live sound, studio recording, and audio production experience to land your first engineering role.

Junior Spa Therapist
A junior spa therapist resume example for VTCT Level 3 qualified therapists. See how to present your treatment skills, client feedback, and spa industry experience.

Junior Sports Coach
A junior sports coach resume example showing how to combine a coaching degree, UEFA C Licence, and grassroots football experience into a full-time coaching career.

Junior Sports Events Coordinator
A junior sports events coordinator resume example for sports management graduates. See how event logistics and participant numbers make your resume stand out.

Junior Sports Marketing Assistant
A junior sports marketing assistant resume example showing how to combine a cricket foundation placement, social media growth, and a sport management degree.

Junior Sports Therapist
A junior sports therapist resume example with clinical treatment numbers, pitch-side experience, and SST membership for new graduates.

Junior Stage Manager
A junior stage manager resume example with prompt book experience, production counts, and cue calling from a Theatre Studies graduate entering professional stage management.

Junior Supply Chain Analyst
A junior supply chain analyst resume example with Honda UK placement and inventory optimisation experience.

Junior Sustainability Consultant
A junior sustainability consultant resume example for environmental science graduates. See how to present carbon auditing, consultancy internships, and environmental volunteering.

Junior Sysadmin
A junior sysadmin resume example with Linux server management, Active Directory experience, and CompTIA certifications from an IT graduate entering systems administration.

Junior Systems Administrator
A junior systems administrator resume example for graduates. See how to present server management, Active Directory, and CompTIA certifications to land your first sysadmin role.

Junior Tax Adviser
A junior tax adviser resume example with placement experience at a regional accountancy firm and ATT study.

Junior Tax Associate
A junior tax associate resume example for tax and accounting graduates. See how HMRC work experience and ATT progress help you stand out to employers.

Junior Technical Writer
A junior technical writer resume example for graduates. See how to present documentation experience, API writing samples, and open source contributions to land your first tech writing role.

Junior Telecoms Engineer
A junior telecoms engineer resume example with fibre optic network experience, OTDR testing skills, and placement at Openreach.

Junior Textile Designer
A junior textile designer resume example with print design projects, client commissions, and weaving skills from a Textile Design BA graduate entering the industry.

Junior Tour Guide
A junior tour guide resume example for tourism graduates. See how to present your guiding experience, customer satisfaction scores, and language skills for the UK tourism industry.

Junior Training Coordinator
A junior training coordinator resume example with LMS administration experience, session coordination numbers, and L&D placement experience.

Junior Transport Engineer
A junior transport engineer resume example with traffic modelling experience, ARCADY proficiency, and CIHT membership.

Junior Travel Agent
A junior travel agent resume example with Barrhead Travel placement and Amadeus GDS experience.

Junior Travel Consultant
A junior travel consultant resume example for tourism graduates. See how to present booking experience, GDS skills, and destination knowledge to impress employers.

Junior Treasury Analyst
A junior treasury analyst resume example with Airbus placement experience and cash management skills.

Junior UX Designer
A junior UX designer resume example for recent graduates. Learn how to present your user research, wireframes, and design projects to secure your first UX role.

Junior Video Editor
A junior video editor resume example for recent graduates. Learn how to present post-production experience, personal projects, and editing skills to land your first editing role.

Junior Visual Merchandiser
A junior visual merchandiser resume example for graduates. See how to present display installation experience, retail knowledge, and trend research skills to land your first VM role.

Junior Warehouse Supervisor
A junior warehouse supervisor resume example for graduates. See how to present team leadership, process improvement, and logistics experience to land your first warehouse supervision role.

Junior Web Designer
A junior web designer resume example with responsive site builds, client projects, and Figma prototypes from a Web Design graduate starting their career.

Junior Web Developer
A junior web developer resume example for graduates. See how to present client work, freelance projects, and performance optimisation to land your first web development role.

Junior Welder
A junior welder resume example for welding course graduates with coded welder certification. See how to present your welding processes, materials experience, and test certifications.

Lab Research Assistant
A lab research assistant resume example for science graduates. See how to present laboratory skills, research placements, and academic projects to land your first research role.

Learning Mentor
A graduate learning mentor resume example with pastoral support, attendance intervention, and pupil mentoring experience. See how to present your skills for learning mentor roles.

Marketing Intern
A marketing intern resume example for recent graduates. Learn how to showcase campaign results, social media metrics, and university marketing projects on your resume.

Mental Health Nurse
A newly qualified mental health nurse resume example showing how to present psychiatric placements, therapeutic skills, and NMC registration for your first Band 5 role.

Music Teacher
A graduate music teacher resume example with PGCE, QTS, and classroom music teaching placements. See how to present your performance and teaching skills for music teacher roles.
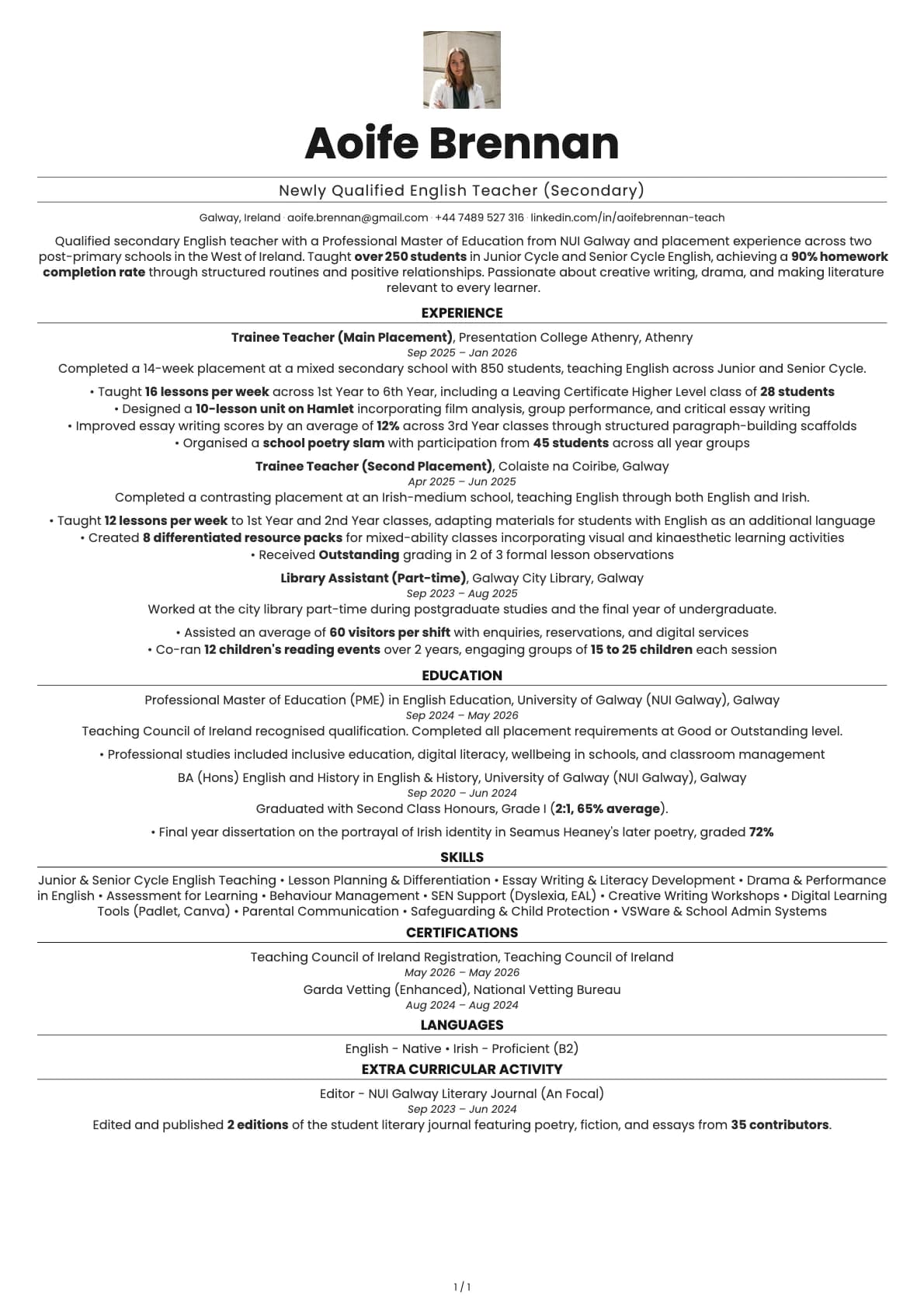
Newly Qualified Secondary English Teacher
A newly qualified secondary English teacher resume example with placement experience, student outcome data, and Teaching Council registration.
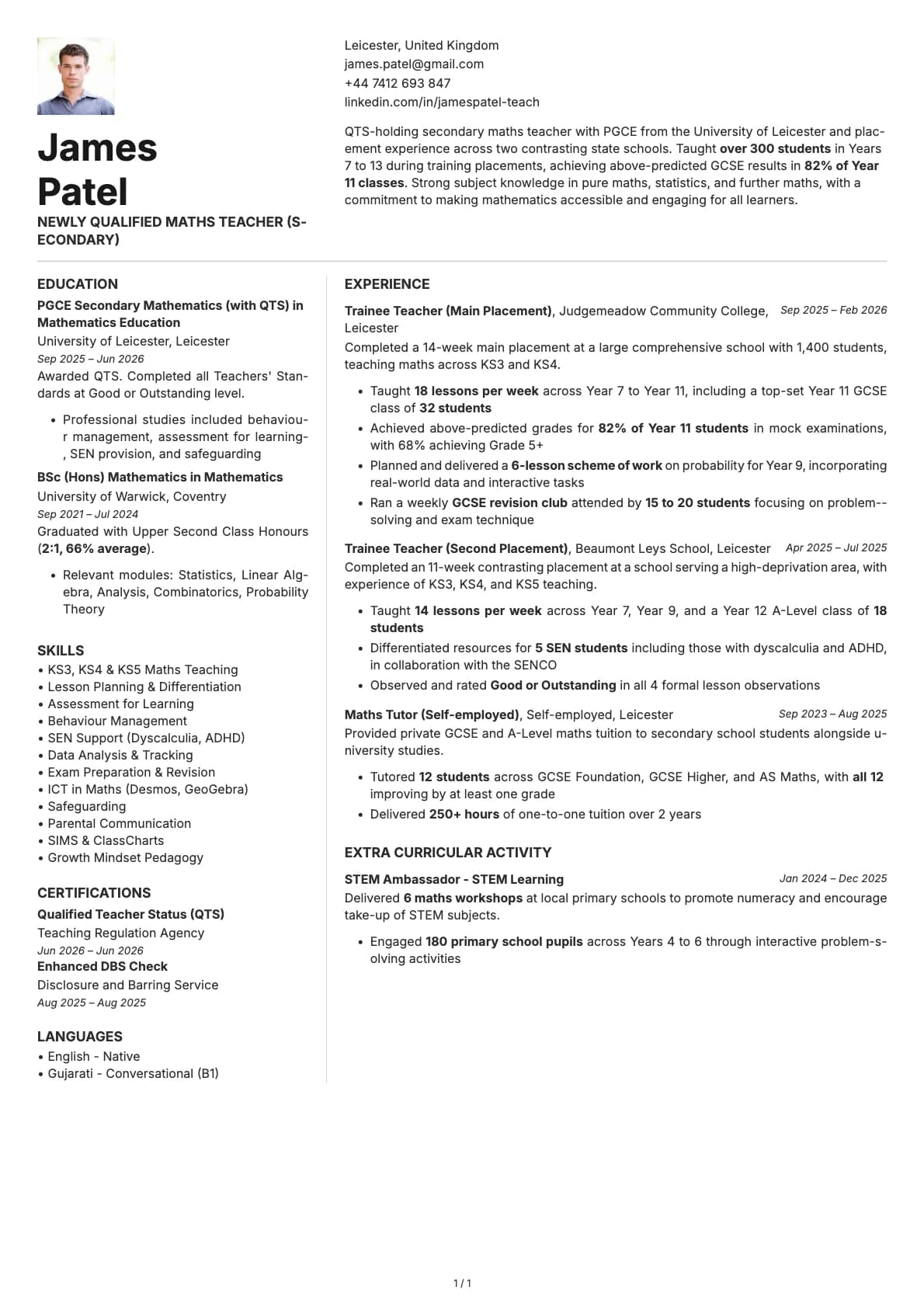
Newly Qualified Secondary Maths Teacher
A newly qualified secondary maths teacher resume example with PGCE placement experience, student outcome data, and QTS for ECTs.
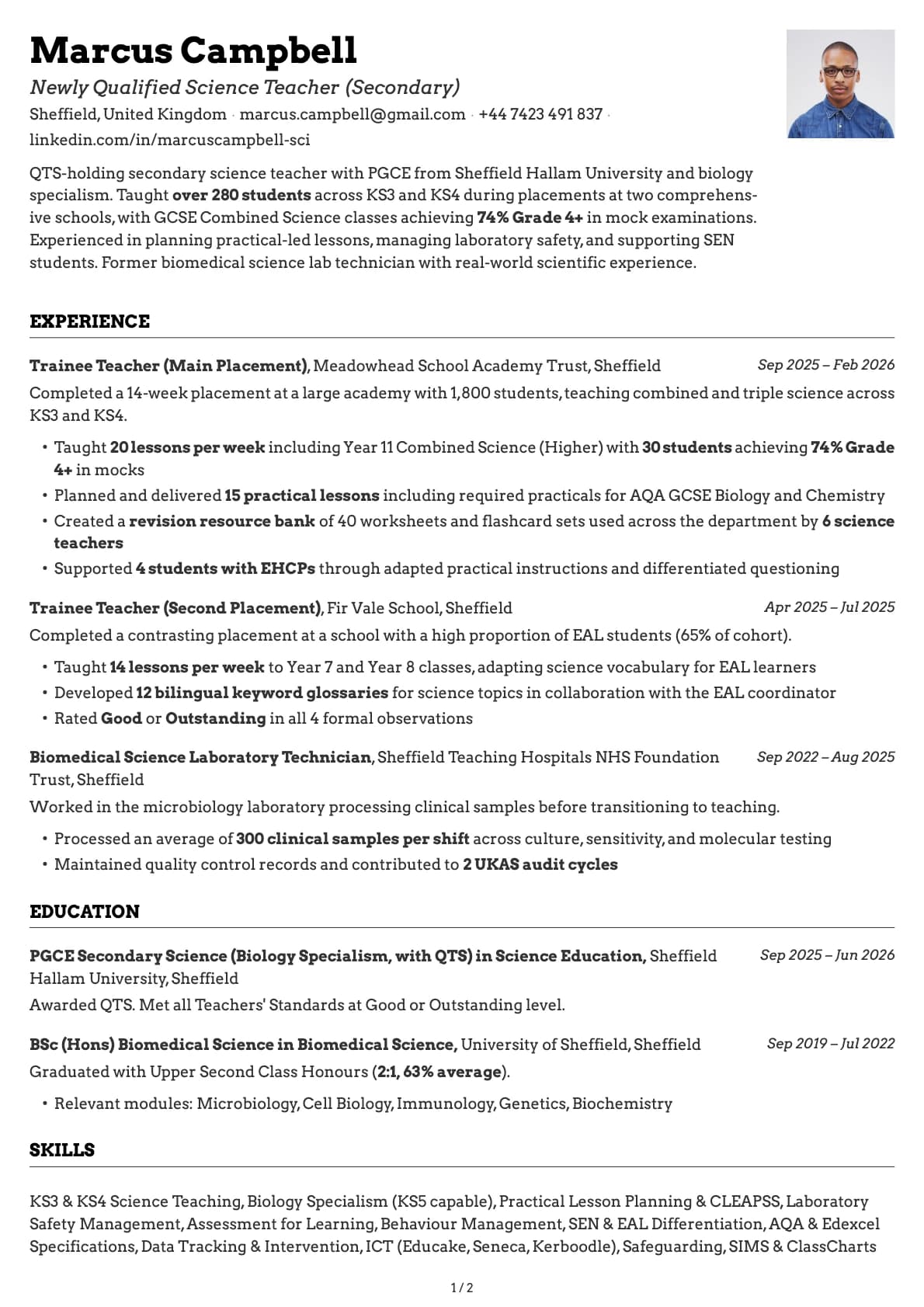
Newly Qualified Secondary Science Teacher
A newly qualified secondary science teacher resume example with PGCE placement data, GCSE results, and practical lesson experience for ECTs.

Newly Qualified Teacher
A newly qualified teacher resume example with school placements, QTS, and classroom experience. See how to present your training to stand out in NQT applications.

Paediatric Nurse
A newly qualified paediatric nurse resume example showing how to present children's nursing placements, family communication skills, and NMC registration for your first Band 5 role.

PE Teacher
A graduate PE teacher resume example with PGCE, QTS, and Key Stage 3/4 teaching placements. See how to present your coaching and teaching experience for PE teacher roles.

Pharmacy Intern
A pharmacy intern resume example for recent graduates. See how to present your dispensing experience, clinical placements, and patient interaction skills to land your first pharmacy role.

Pharmacy Technician
A pharmacy technician resume example for newly qualified candidates showing how to present GPhC registration, dispensing accuracy, and clinical skills for NHS and community pharmacy roles.

Physiotherapist
A physiotherapist resume example with NHS placement experience. See how to present clinical placements, patient outcomes, and HCPC registration on your first CV.

Plumber's Mate
A plumber's mate resume example for apprentice plumbers with NVQ Level 2 qualifications. See how to present your practical plumbing experience for your first employed role.

Pre-registration Pharmacist
A pre-registration pharmacist resume example showing how to present your MPharm degree, clinical placements, and GPhC registration progress for your foundation year role.

SEN Teaching Assistant
A graduate SEN teaching assistant resume example with SEND placement experience, EHCPs, and autism support. See how to present your specialist skills for SEN TA roles.

Teaching Assistant
A teaching assistant resume example for recent graduates. See how to present your classroom experience, volunteer work, and education degree to get hired as a TA.

Trainee Accountant
A trainee accountant resume example for recent graduates. See how to present your AAT progress, placement experience, and bookkeeping skills to land your first role.

Trainee Farm Manager
A trainee farm manager resume example showing how to combine an agriculture degree with hands-on mixed farming experience on a 600-acre family operation.

Trainee HVAC Technician
A trainee HVAC technician resume example for graduates entering the heating, ventilation, and air conditioning trade. See how to present your F-Gas certification and refrigeration skills.

Trainee Mining Engineer
A trainee mining engineer resume example with underground mine placement experience, Deswik proficiency, and IOM3 membership.

Trainee Quantity Surveyor
A trainee quantity surveyor resume example for QS graduates on the RICS APC pathway. See how to present your measurement skills, cost management experience, and professional development.

Trainee Site Manager
A trainee site manager resume example for construction management graduates. See how to present your BSc, CITB qualifications, and placement experience to land your first site role.

Trainee Solicitor
A trainee solicitor resume example for recent law graduates. Learn how to present your law degree, vacation schemes, and pro bono experience to secure a training contract.

Trainee Store Manager
A trainee store manager resume example for retail graduates. See how to present team leadership, sales targets, and merchandising experience to land management schemes.

Trainee Tax Inspector
A trainee tax inspector resume example showing how to combine a Deloitte internship, top taxation grades, and an accounting degree into a Revenue Commissioners application.

Trainee Warehouse Manager
A trainee warehouse manager resume example for logistics graduates. See how to present your warehouse management systems experience, forklift licences, and operational KPIs.

Youth Offending Officer
A youth offending officer resume example for criminal justice graduates. See how to present your placement experience, case management skills, and youth justice knowledge.

Youth Worker
A graduate youth worker resume example with community youth work placements, safeguarding, and programme delivery. See how to present your experience for youth work roles.
Related articles
Career Gaps Don't Scare Recruiters Anymore. Bad Explanations Do.
84% of hiring managers look for growth stories, not perfect timelines. Career gaps aren't the problem. Leaving them unexplained is.

Career Pivots in 2026: How to Rewrite Your Story Without Starting Over
Changing careers doesn't mean starting over. Reframe your experience, highlight transferable skills, and build a resume that tells your new story.

The Cover Letter Isn't Dead. But the Old One Is.
The generic cover letter is dead. Good. But 83% of hiring managers still read the specific ones. The kind that couldn't have been written for anyone else.